As you may or may not know, Microsoft recently patched a vulnerability "CVE-2019-0708" named "BlueKeep" in the RDP protocol. This vulnerability allows attackers to run commands, programs, etc. directly on the affected system without having to authenticate. An ideal payload for a hacker in such attacks would be ransomware.
We want to warn you, and we advise you to check whether you have an affected system immediately. And if so, patch the affected system as soon as possible.
The vulnerability is especially dangerous for computers directly exposed to the internet. But remember: If a vulnerable internet gets exposed, the server or client gets infected, and that same machine can communicate to other servers and clients on your network. The attacker will then have all the access needed to infect your whole network.
Affected systems:
- Windows Server: 2003, 2008 and 2008 R2.
- Windows Client: XP, Vista and 7.
Mitigation:
- Make sure you catch up on all security updates for Windows.
You can read more about the vulnerability here:
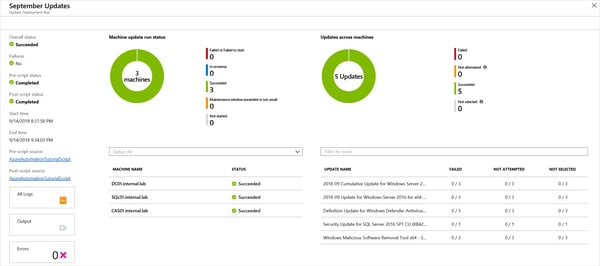
Automatically patched Windows Server
This is an excellent opportunity for us to tell you that Windows Server can be automatically patched on a schedule using Azure Update Management for pennies or less. It works for both on-prem and in Azure servers, using Automation Account with the Windows Server agent and Log Analytics. The only prerequisite is that you run Windows Server 2008 R2 or newer with .NET Framework 4.6 or later and that TLS 1.2 enabled. Contact us if you want more information about this solution.
We'd also like to remind you of following end of life dates for various Windows versions:
Stay safe!
.jpg)
.jpg)
.jpg)